 My article “How To Reduce the Risk Of Getting Scammed and Owned Online” educates you about a variety of attacks you may encounter while browsing the Internet, how to recognize those and as a result avoid being compromised. I recommend you read it first, if you haven’t already done so, as it will help you to understand the main types of attacks and what the perpetrators gain from each, and how do these affect you and those electronically connected to you (friends, family and co-workers).
My article “How To Reduce the Risk Of Getting Scammed and Owned Online” educates you about a variety of attacks you may encounter while browsing the Internet, how to recognize those and as a result avoid being compromised. I recommend you read it first, if you haven’t already done so, as it will help you to understand the main types of attacks and what the perpetrators gain from each, and how do these affect you and those electronically connected to you (friends, family and co-workers).
I wrote this dedicated article for attacks performed via email, since email is the main source of online scam. It is so, because, it’s easy to spoof a sender identity and as a result an email in your Inbox is often considered more trustworthy, than a random website you may visit.
Having my email address listed on my websites since 1999, it has probably made into all possible spammer and scammer databases, and I receive hundreds and at times thousands of unwanted emails daily. As a result of this I have a great collection of bad email I can study and share the insights from that study with you. The examples I use in this article all come from spam email I have received in the last few days. Luckily, my fine-tuned spam filters catch 99.5% of that undesired email, so only 1-2 of those make it to my Inbox daily.
Table of Contents
Sender Information Can Be Easily Faked
Just like I can mail you a parcel and write that it’s from Santa Claus, I can send you an email from Santa and you won’t know the difference.
I can instruct my email client to have my identity set to “Santa Claus <santa@northpole.com>” and if I send you an email it will have:
From: "Santa Claus <santa@northpole.com>" Subject: No gifts for you this year Try harder next year! Santa
Most of the time all you need to do to tell that the email is not from who they claim to be is to look at that From: field of the email in question. Here I will use Paypal as an example, since there are so many phishing emails related to Paypal services.
Here are a few examples where you can instantly tell that these aren’t emails from Paypal:
From: "PayPal Security Update no-reply@paypal.com" <info2015@powtex.com>
Surely, they inserted “no-reply@paypal.com” into the free text identity part of the email, but powtext.com is not Paypal.
Or the following one:
From: Support <admin@server.chinanetrix.info>
Here you can clearly see that it’s not coming from Paypal.
So now you know how to tell most of the scam/phishing emails coming from money-related and other online services.
There is a much smaller percentage of phishing emails where you cannot tell from the From: header that it’s not an email form Paypal. It may look like:
From: "service@intl.paypal.com" <service@intl.paypal.com>
but it will not be a legit email from Paypal. If that’s the case, unfortunately, there isn’t an easy to way to tell. Below between the two lines I will provide information on how to do that for more advanced users. But do not despair, later in this article I will give you a second, even easier to use technique for identifying illegitimate emails. The second technique is to look at which website the perpetrator is trying to send you.
Non-advanced users please now skip over the next section between the two horizontal lines.
<– Advanced explanation starts here –>
If you are an advanced user and you know how to tell your email software to show you all email headers, then you can usually quickly tell whether the sender is indeed who he is. (scroll down a few lines if you don’t know how to do that, where I will show another way)
Consider this email:
From: "service@intl.paypal.com" <service@intl.paypal.com> Received: from mx0.slc.paypal.com (mx1.slc.paypal.com [173.0.84.226]) Subject: You've got money
Here the From and Received headers match at their domain name level, so this was indeed sent from Paypal.
Note that there are several Received: headers in each email and you need to look at all of them.
And now consider this one:
From: "PayPal" <service@intl.paypal.com> Received: from FIRM-TS006.FIRM.local (ip-78-137-145-191.dub-3rk.metro.digiweb.ie) Subject: Your account has been temporarily suspended
Clearly that’s a fake paypal email, since From and Received domain information headers don’t match.
Luckily probably about 95% of phishing email senders don’t bother to obfuscate their origin, so most of the time you don’t need to look at uncommon email headers as explained in this section.
<– Advanced explanation ends here –>
Never Reply To Or Act On Emails You Are Not Sure About
The first rule is that unless you’re certain who you received an email from and you really really need to get in touch with that person, do not reply to any such emails. If you do, they will first know you exist for real (there are many dead email addresses) and they will re-sell your email address to many other scammers, and you will get hundred times more scam emails.
Second, anything you will tell in your reply will be used to further perpetrate their con activity against you. Before you reply to them they usually know nothing about you. If you reply even once they now know a lot more about you.
If unsure, the best action is to instantly delete such email. Most banks who have any security sense will never conduct any business with you by email. Always call your bank instead, if you believe your bank really contacted you via email. You can also open your Internet browser and log in into your online service/bank, but that’s not 100%-full proof, since if your computer is owned you could be tricked into logging into a site that looks like your bank, but it’s not. So phone will be your best bet. That is of course if you know your bank’s real phone number. There are scammers who do scam over phone too.
I trained my dad to always forward me any emails he is not sure about and 99% of the time my reply is a single word: Delete.
If you are a polite person and have no heart to just delete an email without doing anything about it, it’s important for you to know that email is an unreliable media. A huge number of emails (including legit ones) never reach their destination, due to various filters and blocks that Internet Service Provider companies use in order to keep the amount of bad email manageable. Therefore, usually senders cannot know whether you received the email they sent to you or not (albeit there are ways to circumvent that) and therefore if it’s a real person with legit purpose they will find another way of contacting you. Thus, I repeat, if unsure, it’s safe to delete any email that comes to your Inbox.
Scam Emails From Your Family, Friends and Acquaintances
Every so often I get an email like the following one:
=================================== good evening Stas http://bit.ly/2hblkjasd8fGWy1 Joe ===================================
No story, no context, just enough information to establish familiarity (it’s from Joe, whom I probably know since I’ve communicated with Joe before and thus my email is in his address book) and a link (I scrambled the original scam link). Of course the scammer can be more elaborate and write a real story enticing me to click on the link, but it’d be tricky since he will have to know a lot more about the sender or a the recipient (me) to create a believable story. But this too is possible if the potential payoff to the con artist is worth it.
Now, this kind of scam happens if a scammer either broke into your email account (yahoo, gmail, etc.) by keylogging[1] the login/password you used to access your email account in an Internet cafe, while you were traveling or he hacked your computer and he has a keylogger installed on your computer, or perhaps you use Outlook or some other desktop application and then the address book information is right there on the computer without needing to break into your online email account.
footnote 1: keylogger is a virus/malware program that logs everything that’s being typed on the keyboard and then this information (including passwords) gets sent to the person who broke into your computer.
The bottom line is that the hacker (most of the time it’s a malware) has now established a link between the hacked email account owner and all people in that person’s address book. It can then quickly analyze who this person emails the most (friends, family, etc.) and then send them an email with a link to a scam site like I have shown above. It may use a fake sender information, but most of the time they use the hacked person’s email account and send the email from there, in which case all the information in the email will be completely legit (i.e. appearing as a real person you know).
What can you do if this happens to you? If you were not the one who has been hacked, but instead your email address was in the address book of the hacked person. First, don’t click on any links in emails sent from that person. Second, tell the hacked person that his email account or computer has been compromised. Ideally not through the same email address since the perpetrator could be smart enough to scan incoming email and automatically delete any such alerts. Best is to use his phone or some other channel where you can establish a real person to person contact.
If you were the one, who has been hacked, truly there is little you can do. The hacker already has your address book and you can’t take it away from him. You definitely need to change your email account’s access password, but you must do it from another computer. Ideally a computer that is safe, which can be very tricky to find these days. Most likely a computer running Linux will be the best bet. Or walk into a computer service company, ask to use their computer, which is likely to be safe (but not guaranteed). The problem is that if you changed your password safely and your computer still has the key logger malware on it, the hacker will get your updated password as soon as you login into you email account next time. Really you need to completely reinstall your computer to get rid of any hidden viruses that your antivirus software couldn’t catch. But if you run Microsoft Windows it’s a matter of hours and often minutes after going online before you get re-infected again, and this after you spent hours and perhaps days reinstalling everything. Switching to Linux operating system is the safest solution, not only because it’s much more secure than Windows, but primarily since it has the smallest user base and thus isn’t very attractive to hackers, who can make much more damage/money attacking very wise-spread systems like Microsoft Windows. Recent Mac systems run underneath a Unix-based variant, so in theory they are as secure as Linux. But since Mac is much more popular than Linux, hackers are more likely to attack a Mac before they will go for Linux. But no system is truly secure, it is all risk management.
I empathize with you, as this is a very difficult problem and there are no really easy solutions here. But at the very least having the awareness of this issue may be helpful to you and those digitally connected to you. I wish I knew of a magical solution to share with you, but I don’t other than unplugging your computer from the Internet.
Never Click On Anything In Emails You Are Not Sure About
If you received an email that seems to be coming from your bank or an online service and it’s asking you to do something, e.g. update your password, fill out some form, or alerts you that your account got locked or robbed. Ignore the rest of the email and call your bank or online service. They will tell you what’s happening for real. Do not be afraid to be a nuisance, on the contrary, the clerk on the other side is most likely going to thank you for being vigilant and security conscious. Banks lose a lot of money to online fraud.
Most of the time it’s easy to identify a scam/fraud/phishing email by simply hovering the pointer over the link the email is trying to incite you into clicking. When you do so, most email clients will show you where the link is really taking you and not what the text suggests it to be. Here is an example from a recent Paypal email (personal data removed):

As you can see that if I hover with my mouse over the blue link “preference centre” (where the first red arrow is pointing), the status bar at the bottom of the image (where the second red arrow is pointing) shows:
https://www.paypal.com/myaccount/settings/notifications?ppid=[...].
So this link is indeed pointing back to paypal.com and it’s relatively safe to assume is valid.
Do be careful though as a scammer could arrange all the links pointing to the correct service and swap only that one crucial link to take your to their fraudulent website. Here is an example of this exact case:

Hovering over the “Recover them here” shows us a real Paypal address. So far so good.
However, if I hover over “Login Now” button:

Ouch, this is no longer Paypal. If you look at the status bar at the bottom of the image (second red arrow), this is the scam/phishing/malware website[2] the sender wants you go to. You can be sure that the destination website will look like paypal.com (it is so easy to copy any website’s looks) and will gladly take your ‘login’ and ‘password’ so that you can see what’s wrong with your account. Once you type those in, it’ll give you some kind of an error, suggesting to come back later, or even redirect you to the real Paypal website. Except now the perpetrator has your login and password information and can login into your real Paypal account and do whatever he wants with your money.
footnote 2: I hope you will not type up the hacker’s website link and be curious to check it out unless you know you are doing that on a secure system.
Another type of such misleading linking is inserting the word Paypal into the website address. Here is an example:

As you can tell at the very bottom of the image, the link indeed contains the word paypal, but instead of using paypal.com domain name it uses some IP address, which will never be paypal.com’s address. Surprisingly most scammers don’t bother to be really sneaky, most of the time they won’t even have the word paypal in the phishing website address.
Some very sneaky ones can create a destination address like: http://somefakewebsite.com/paypal.com/i-own-you – so it even contains paypal.com in it, except in the wrong place. You want to see https://www.paypal.com/ or https://www.paypal.ca or a few other valid variations to know that the website is really a Paypal website.
Here are a few other examples of enticing emails:
If you were able to follow and understand the above you will now be able to instantly tell 99% of scam attempts in your Inbox by checking the From: address and where the “Action” link is pointing you to. But perhaps you found it a way over your head. Do not dispair! If you didn’t understand it — never click any links in the emails you receive, instead call the company on the phone you know to be valid for that company. I.e. you didn’t find it in that same email, but instead you went to a real website typing paypal.com into your Internet browser and finding their phone number there. And even that can be not 100% safe, if your computer is compromised and the hacker tricks your Internet browser to go to another similar looking website instead. So even better use the good old printed Yellow Pages book. Google can be useful too, except even Google makes spectacular misinformation mistakes at times (see at the end of this article).
Don’t Open Questionable Email Attachments
Attackers often put malware in an email attachment and try to get you to open it.
Here is an example:
Hello stas, You are going to be billed USD 2,230.50 on your Mastercard card soon. View attachment to avoid it. Password is 5558
Here they use an attachment that’s a virus program, and use the scare tactic to make me open the attachment. They also give me a password to make it look more legit (i.e. nobody else but you will be able to open that attachment, so they confide in you).
Most of the time they guess wrong, (i.e. I don’t have a Mastercard), then it’s easy to delete. But if they happen to guess right be careful to contact your bank by phone if you’re concerned and don’t open any such attachments. Your bank will never send you any such information by email.
Nigerian Scam (Advance-fee scam)
There is a whole category of scam emails that were invented by a few brilliant social engineers in Nigeria, and even though now it’s used by many scammers, this type of scam is often referred to as a Nigerian Scam. Properly this is called Advance-fee scam, and apparently it has been used as early as 1922. The Internet has just made it much much easier to perform.
The scam’s ploy is very simple. The senders is asking your help to transfer a huge amount of money (usually around $1 million) out of their country, offering you an insanely large commission (e.g. $100,000). The only trouble is that they need, say, $10,000 to pay the lawyer to do the transfer and they ask you to pay that, since they have no access to that $1 million before they pay the lawyer fee. Usually it involves a widow or some other type of situation which will help to create trust.
Just today I received:
Hello, Compliment of the day to you. I am Mrs Natacha William; I am sending this brief letter to solicit your partnership to transfer $19.5 million US Dollars. I shall send you more information and procedures when I receive positive response from you. please send me a message in my Email box and here is my (natachal_w@foxmail.com) Thanks Best Regards, Mrs Natacha William
Clearly you want to trash any such emails and never reply to them. Even if you’re a super polite person and you just have to say, Thank you, but no Thank you. Or if you want to tell them that you can see through them. Do Not! Any reply will validate your existence and they will get you elsewhere.
Often they try to speak to your heart and goodwill, consider:

You can see other elements of establishing trust. For example see the disclaimer at the end that is usually used by real businesses.
Here are a few variations on this type of scam.
Good day. Urgent - help me distribute my $12 million to humanitarian. this mail might come to you as a surprise and the temptation to ignore it as unserious could come into your mind but please consider it a divine wish and accept it with a deep sense of humility. I am mrs Helen George and I am a 61 years old woman. i am a South African married to a Sierra Leonia. ... much more trimmed ...
another one:
Compliment of the day, How is your day. I am Mrs.Siti Zakaiah from Malaysia, I am writing to let know you that I am a widow with the amount of $5.3M buisness proposal for you. the fund was left by my late husband and the bank inform me to present his business partner before the fund will be released.
Note that they smartly use typos and grammatical errors, to appear as if it were a real person, whose native language is not English.
Yet at times the most genius approach the scammers use to get you into talking is by sending an email with just:
Can we talk ?
Since you don’t have any context, you might be curious to reply to ask for more information and that’s where they can get you, all because you replied once and they will then use your human nature against you.
And of course see a dedicated article on how I almost got scammed just recently, on a much smaller scale and the scammer used the service I offer as a bait. The article includes the complete exchange of emails so that you can hopefully learn from it and not fall for the creative variations of the Advanced-fee scam.
I Love You Already Scam
If they can’t get to you via your greed, they will try your heart. If you’re a man and are lonely they are likely to get you via emails like this:
Hi, honey! The main thing for us is to trust and to hope. When I close my eyes, I see you. I send you a lot of kisses. Write me please! My email fake_girl_name_here@rambler.ru
Trust me, there is no girl behind this email. It’s an automatic software sending you this email and if you reply, while it’s quite possible that there will be a female fraudster behind the scheme, I have to disappoint you and tell you that most likely it’ll be a guy you will be talking to, thinking it’s a woman.
If you reply, the other side will start romancing you with sexy photos and cries of despair asking for your help. Except all they want is the contents of your wallet and then some.
If you want to participate in online dating, initiate this yourself by going to a credible dating website. Of course that doesn’t guarantee you will be romancing a real woman either, but the probability of that will be much higher. And even if’s a fake profile, those who run it, will not know that you’re gullible and desperate for love, as they instantly do know if you were to reply to such email.
Here are a few other examples:
My dear! How are you? I send you my tender love, my warm embrace and my most passionate kiss-across the miles. I am waiting for your answer! My email vendula7wzkin@rambler.ru
Hello my dear - I've had a web camera with good quality. I'll do what you want for you, long time not seen you in a web camera. My email anetaulrikeuir@rambler.ru
Unsolicited Service Offers
And then there is a huge percentage of spam emails that contain unsolicited service offers.
If you have a website, you’re likely to receive dozens of emails from companies telling you that you website doesn’t rank well on Google and that for a fee they will tell you how to fix that (SEO service), or that the design is broken and they will re-design it for you. Most come from real companies (many come from India) looking for customers. They send the same unsolicited email to millions of people and if 10 take the bait they are happy. So the math works well. Except there are thousands of such companies, each sending millions of such emails daily. That’s not fun. Thank God for email spam filters!
Here is one I received yesterday:
Subject: Loved your site ChestofBooks.com: Read Books Online for Free, would love to guest post for you Hi there, My name is Chris and I run the Nature Sport Central website. I’m writing to you because I’d love to contribute a guest post to your site. I’ve been brainstorming some topics that I think your readers would get a ton of value from:
- 7 Tips for Camping With Kids
- How to make camping with kids fun and relaxing
- How get organized to get the most of out of camping
I’ll make sure the piece overflows with information that can’t be found anywhere else. In exchange I'll be sure to share your site to my social media following (2k+ Facebook, 7k+ Twitter, 3k+ Pinterest & 2k+ Instagram followers). I'm sure you'd get some nice publicity. Let me know what you think and keep up the awesome job with your site! Cheers, Chris Cole
If you look at the subject line (first line), you will see that this is an automated email and not a real person. The spammer software visited my website: ChestofBooks.com, scraped the title of the front page, which contains:
ChestofBooks.com: Read Books Online for Free, would love to guest post for you
and used that to create an email. Perhaps there exists a person by name Chris, who will take over if I were to reply to this automatic probe, perhaps not. But clearly I’m not replying to any such emails and immediately delete them.
Moreover in about two days or so I will receive a follow up email giving me another chance to reply, reminding me of the first email, and sometimes there is a third “final notice”-type of email. Delete them all without thinking twice!
Yet other spammers go even further to make you feel guilty, and they tell you that they already did the work for you even though you haven’t asked them to do so. And so of course you will be curious to see what have they done for you. (curiosity tactic)

and then 2 days later there is the follow up:
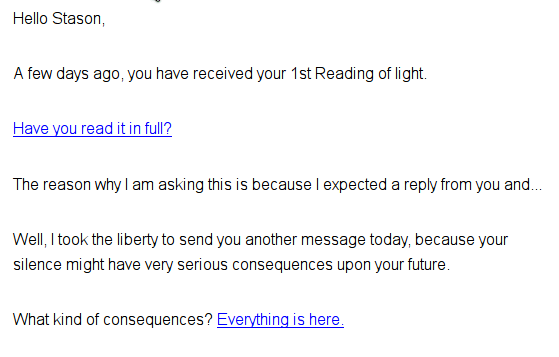
This is no longer a curiosity tactic, my silence lead them to escalate this fraud to fear tactic.
note: I’m so happy that my spam filters keep me clear of this scam, just reading through my spam email folder to give you examples for this articles make me feel yucky.
Granted these unsolicited emails are mostly harmless and just waste our time and our cool at times, but trust me some of those aren’t real service offers but yet another way of a fraudster to get to you.
Faking Trust Tactics
As mentioned in a few places already the spammer will try to get as much information about you as possible and use that in their initial email to gain your trust.
But they are other methods.
- Using prefix Re: in the subject line.
Usually when you send your friend an email with a subject:
Subject: Let's go for a hike
when she replies to you it comes as:
Subject: Re: Let's go for a hike
The email client software does it automatically to indicate that this is a reply (Re:-ply).
Since you’re are unlikely to open an email with a subject:
Subject: Get Your Website First in Google Ranks
as it’s a clear giveaway of what’s waiting for you in the email, they change the subject to:
Subject: Re: Get Your Website First in Google Ranks
Now, it appears as if you have already been having a discussion and now you will feel obliged to open this email.
Similarly FWD: is another type of common prefix that is used by email client software to indicate that the current email has been forwarded to you and not written from scratch. Of course anybody can write anything in their Subject line, so a spammer can use a similar tactic and write:
Subject: FWD: How To Get Your Website First in Google Ranks
Now that makes you think that someone cared enough about you to think to forward this very useful piece of information to you and thus you’re likely to open such email.
2. In the previous section I mentioned another strategy where the spammer will reply to his own email that you hopefully didn’t reply to and try to get to your kindness by making you feel guilty that you didn’t reply to their first email and hope that you will do it this time. And they will do it a few more times, continuing this conversation with themselves and all along encouraging you to feel guilty and act on it out of guilt. Only if you unconditionally delete them all and hopefully not even bother to read the details will they leave you alone (this time).
In a few days they will try a different approach. It will come from a different person/company with different pretext and reasoning, except most of the time it’s the same spammer. But even if it’s a different spammer, what do we care. We delete them all.
If you haven’t yet read it, please proceed to my article “How To Reduce the Risk Of Getting Scammed and Owned Online” to learn about other security risks you will certainly encounter when conducting your online activities, with an exception to email, that’s covered in this current article.
If you think of other common types of email attacks not listed in this article, please kindly use the comments section below to share those with the readers. Thank you.
Tags: email, fake identity, hack, malware, phishing, scam, spoof, virus



Leave a Reply